Azure provides many features to protect our services like Azure WAF, Azure Firewall, and we also use third party products.
Often we set up our firewalls and security appliances like SIEM systems, policies, or even Microsoft areas like Security Center.
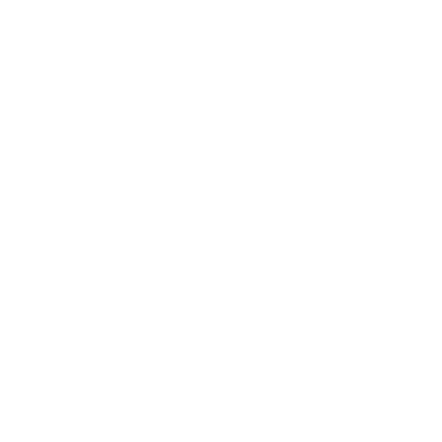
The best method is to create our honeypot and simulate real attacks on our infrastructure.
A honeypot, in computer terminology, a honeypot is a computer security mechanism set to detect, deflect, or, in some manner, counteract attempts at unauthorized use of information systems. (Wikipedia)
It is an excellent practice to have a honeypot, and there are four main reasons for that:
- we provide to newbies hackers something to play with
- we use it to test our security infrastructure
- we use it to train our SOC team
- we use them to educate company people about security threats
We can create different honeypots, each one for specific attacks like SQL injection or XSS scripting or social engineering, or we can use a single honeypot covering many types of attacks.
Initially, I recommend using a more generic one, and we can find many vulnerable websites on the internet like bWapp or Webgoat, and other more, in this post, we will use bWapp.
You can use bWapp on Linux, Windows or in a docker container, and the Linux installation is very straightforward, I like to show you the Windows one because I see many people asking for that and having some significant issues.
Create a virtual machine in Azure, use the Windows 10 operating system.
In the Azure network security group open port 80 and 443, and the 3389 for RDP, remember this is a honeypot, let hacker try an RDP brute force attack, use a robust password, primarily use! Char, which makes it much more complicated.
Download the last version of bWapp for the website http://www.itsecgames.com/
Now install XAMPP for Windows https://xampp.en.uptodown.com/windows/versions, this is the most crucial point, you need to download an old version, I recommend the 5.6.15
Install XAMPP and enable the apache and MySQL service from the control panel
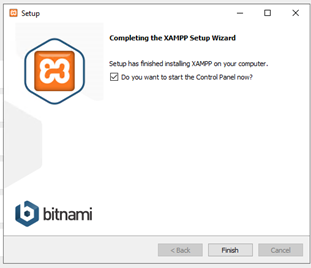
Copy the bWapp folder in C:\xampp\htdocs
Navigate in http://localhost/bWAPP/install.php and execute the installation.
Log into bWapp using bee/bug

I like bWapp because it is one of the best vulnerable websites

Now you can create an image of this VM and put this VM behind a WAF and start testing the WAF rules or more.
There is a lot to speak about this topic, and I will do a session on the 18th of June https://www.overneteducation-eventi.it/azuresecurityday/
During this session, I will show the most dangerous attacks, physicals, and virtual attacks, and some of the most advanced security strategies to protect our Azure infrastructure.